It may also be called an Application Firewall or Next Generation Firewall.
Layer 7 firewalls perform functions at the application level. This means that they will be able to perform functions on network protocols higher than layer 4 and 3 firewalls.
These types of firewalls emerged to revolutionise network security as we have known it up to now. Traditional firewalls are limited to stateful packet inspection and access control rules, but as hackers have become more sophisticated, the threats have become more advanced, so this system is no longer effective. In order to protect a business from constantly evolving threats, the Next Generation Firewall must be able to offer a deeper level of network security.
The key is to ensure that every byte of every packet is inspected, but this must be achieved while maintaining high throughput and low latency to keep high-traffic networks running optimally, combat threats effectively and address increasingly urgent productivity issues.
Enterprises require a deeper level of security and control, which this type of firewall offers. Here are some of the key features:
Cybercriminals often attempt to circumvent IPS by using complex algorithms that evade detection.
The popularity of network access-based applications has exploded in the last ten years, making it more difficult for administrators to monitor user activity and traffic usage by applications.
New malware variants are being developed every hour. Keeping abreast of all these threats with network-based malware protection that uses a constantly updated cloud database is critical to blocking new threats as they emerge.
In other words, a Layer 7 Firewall has the ability to analyse and protect your server or cloud from a much wider variety of attacks because of its analysis capabilities and power. Highlights:
It is the ability of SWPanel to activate and manage multiple layers of Layer 3, 4 and Layer 7 firewalls that filter incoming and outgoing traffic to your server or cloud to ensure full protection against attacks, or even to ensure that your server or cloud is not the attacker.
Note that there are different levels of next-generation security services, each with different capabilities/properties. You can select the one that best suits your needs.
Yes.
Many times when talking about Firewall or protection, we focus on inbound traffic. Solutions such as CloudFlare, Incapsula or WAF applications are based solely on the analysis and filtering of the traffic received by your server or cloud.
But what about the traffic that my server sends, can it be harmful?
Yes, your server can be compromised or have viruses or malware installed inside it and become part of a botnet or be controlled remotely. In these cases, traditional external filtering such as CloudFlare, Incapsula and many others are of no use.
Yes.
With the Next Generation Security of SWPanel and SW Hosting. When we filter traffic, we do it in both directions: incoming and outgoing traffic.
We can protect you against attacks and prevent you from being the attacker. Often, for a company's reputation, it is worse to be the attacker than to suffer the attacks.
This is the great virtue of SWPanel's New Generation security, it protects in both directions.
All the reports, lists, analysis and statistics that the new generation security offers you, will have the analysis of the traffic received and sent.
At all times, you will know whether you are under attack or being attacked. And all this with country-by-country analysis and a worldwide view of the geographical distribution of your attacks.
Enter the name of your server in the top search box of your SWPanel and select it.
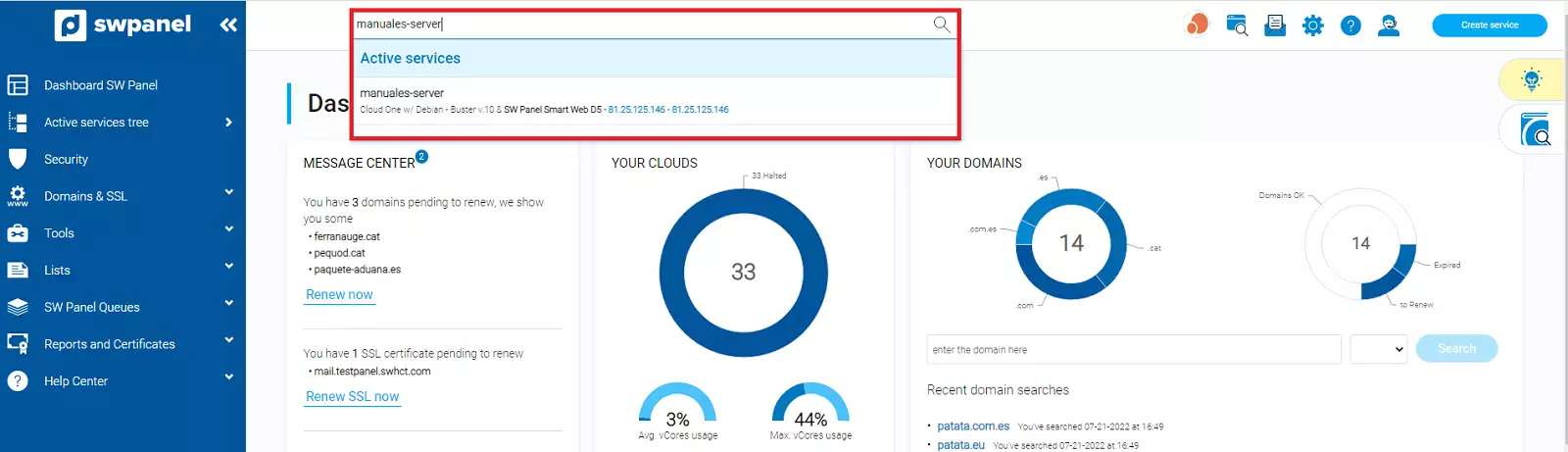
Once selected, SWPanel will show you the Dashboard of this service.
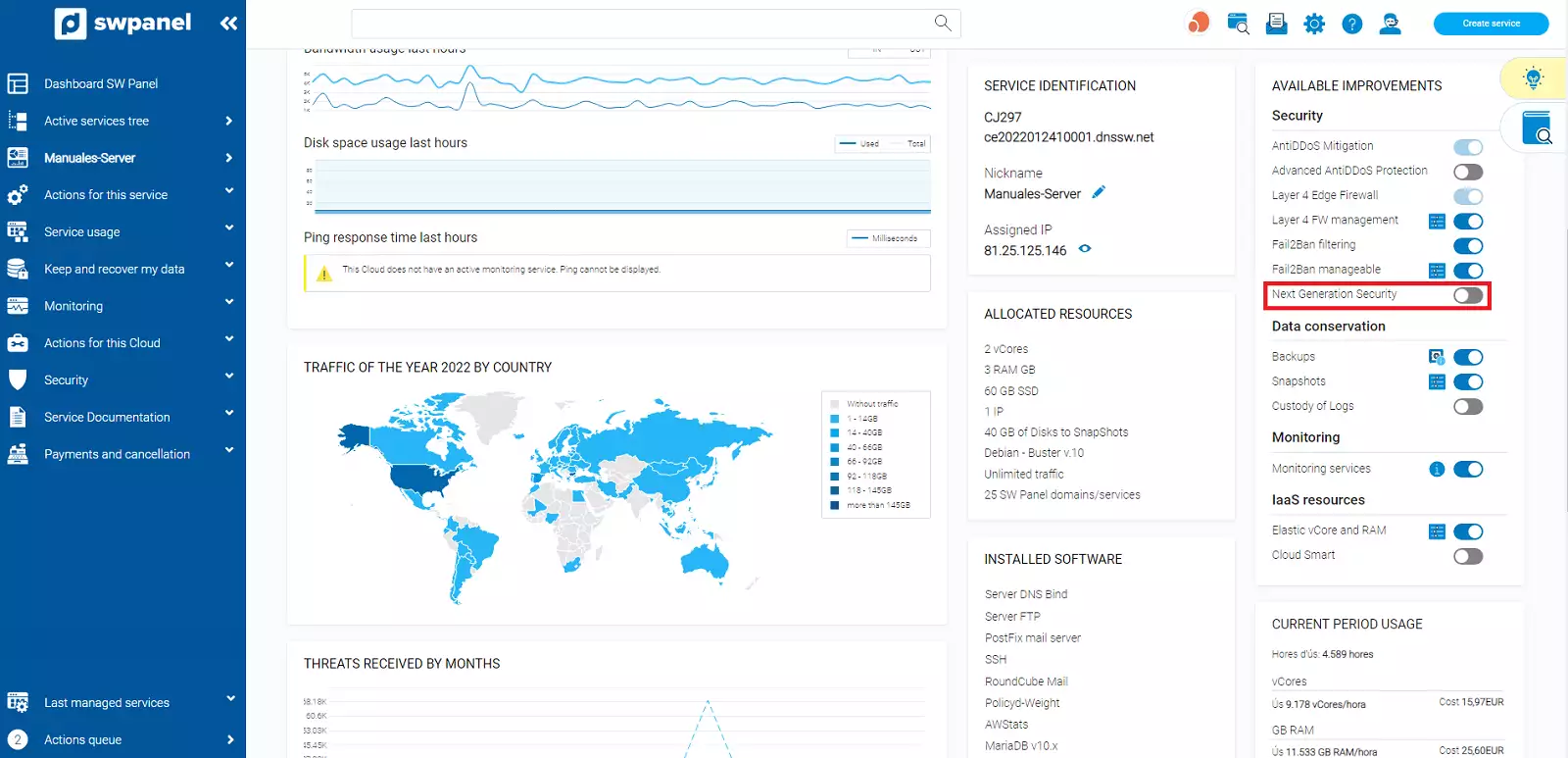
In the Dashboard, you will find the "Available Upgrades" box and in it you will find the Next Generation Security option and a button to the right to enable or disable it.
Move the button to the right to activate it.
Once clicked, you will be taken to the Next Generation Security configuration and activation screen.
On this screen you will be shown a table with the available Next Generation Security subscriptions and each of the details and features of each subscription.
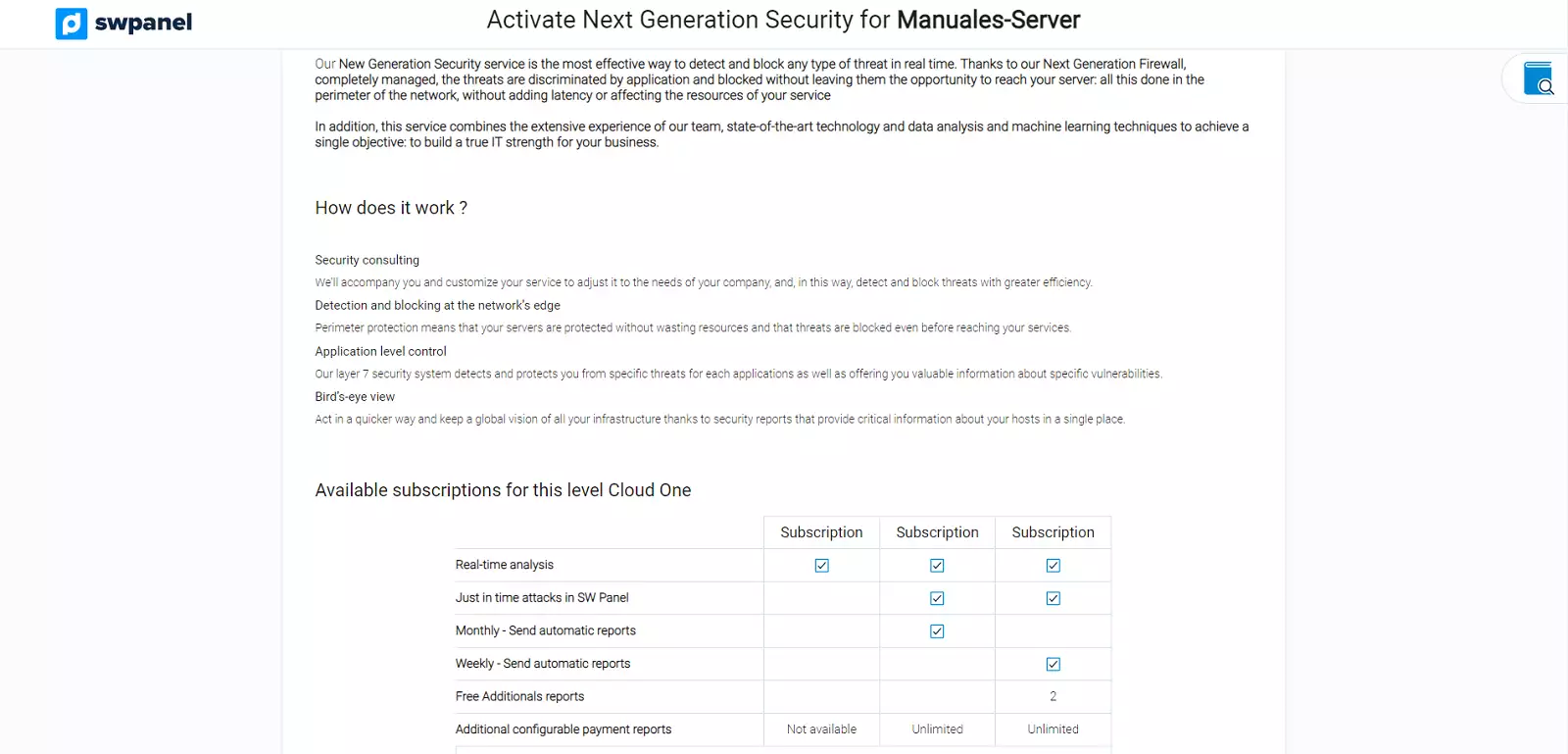
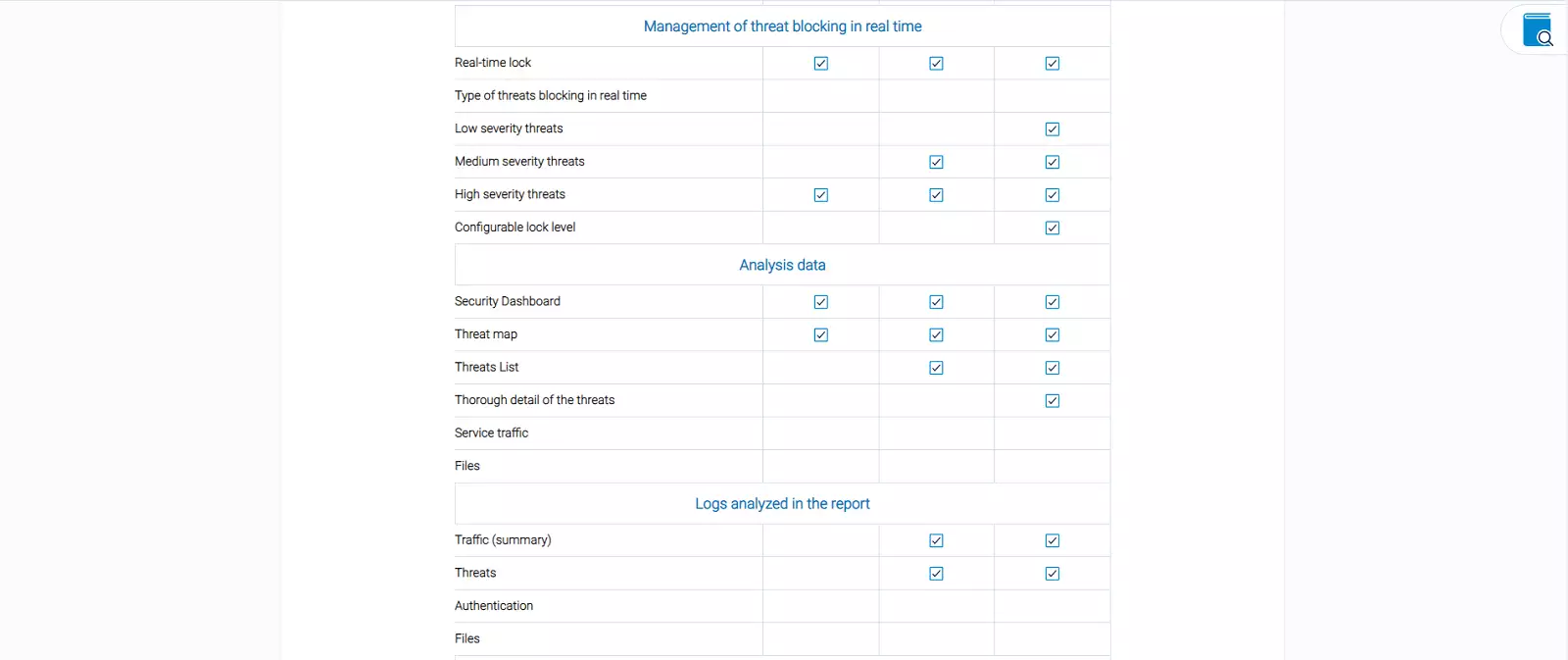
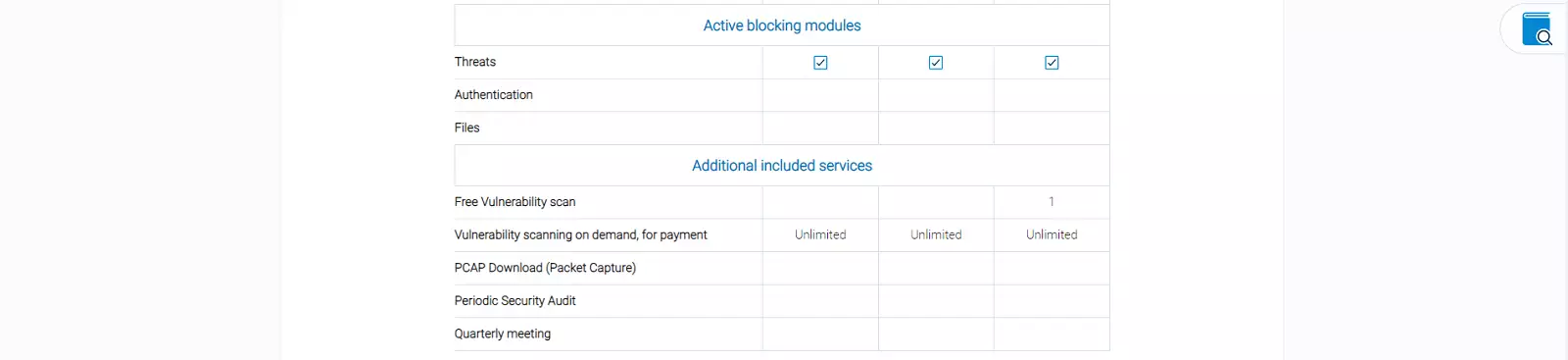
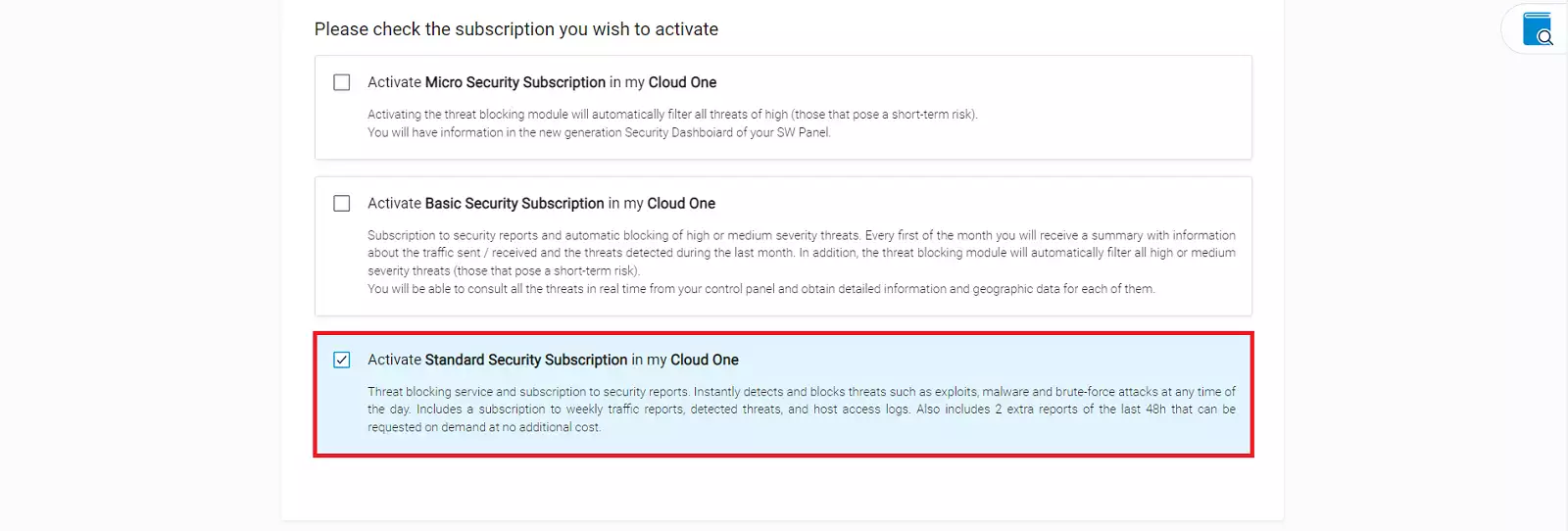
Study and analyse which subscription best suits your needs before activating it.
Once you have decided, check the corresponding "checkbox" to activate this subscription and confirm the activation by clicking on the Activate Now button below.
In a few seconds it will be activated and now the Dashboard of the service will show you the switch in green as you have already activated it.
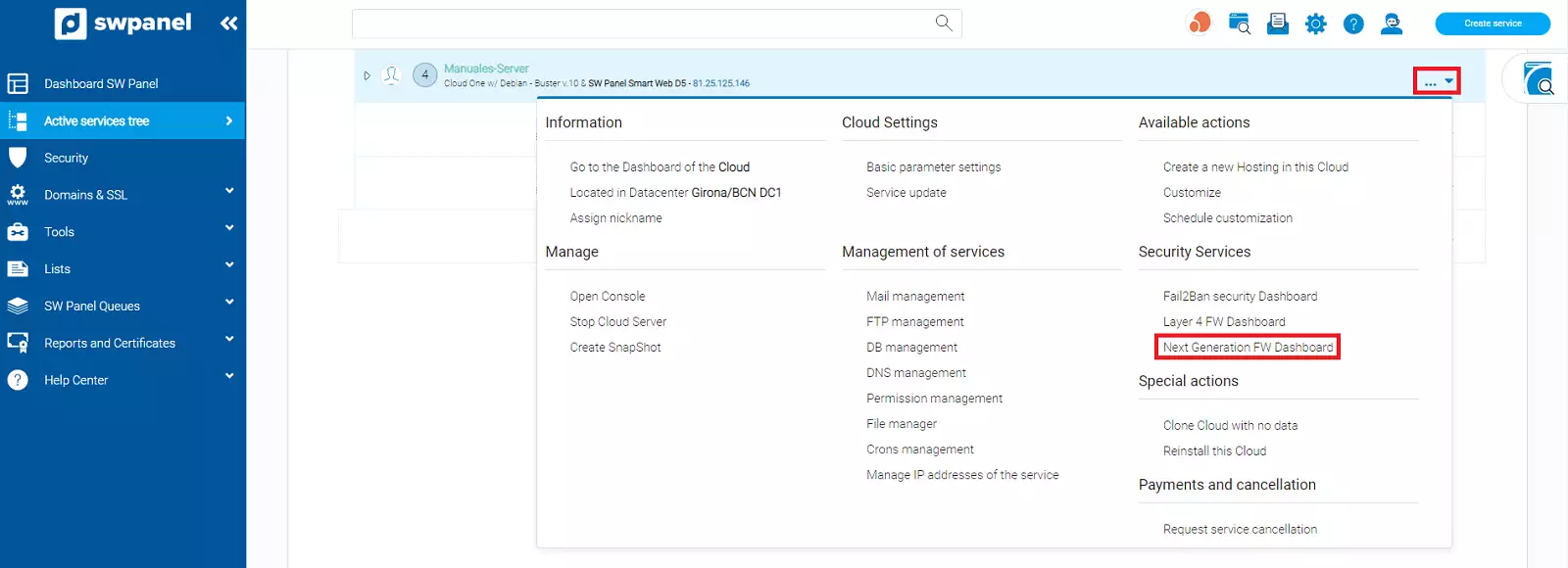
The first step is to access the service tree of your SWPanel.
Find the Cloud or server you want to activate the Next Generation Security and click to open the Manage menu.
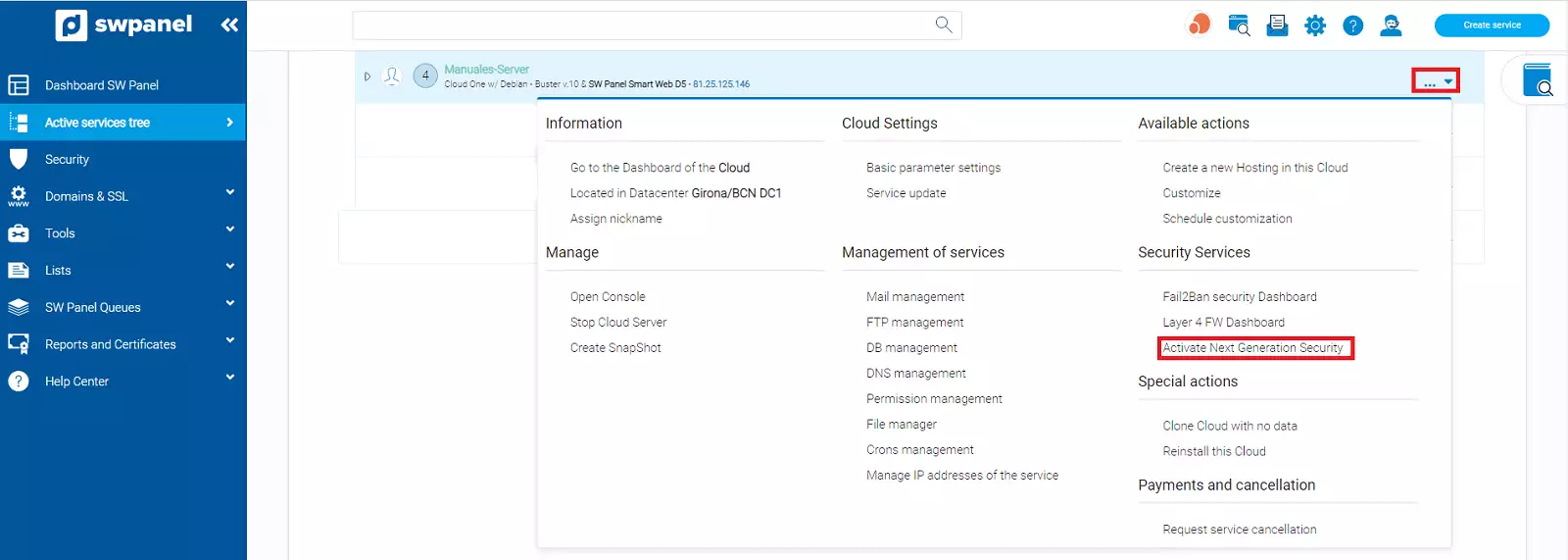
Within the menu you will find the Security Services section, click on the Activate Next Generation Security option.
SWPanel will take you to the Next Generation Security activation screen.
On this screen you will be shown a table with the available Next Generation Security subscriptions and each of the details and features of each subscription.
Study and analyse which subscription best suits your needs before activating it.
Once you have decided, check the corresponding checkbox to activate this subscription and confirm the activation by clicking on the Activate Now button below.
Just like that, in a few seconds it will be activated, and now the Dashboard of the service will show you the switch in green as you have already activated it.
Once the new generation security has been activated, in the Security section that you will find on the left side of the Dashboard of the server on which you have activated the security, you will see the FW New Generation menu and its different sections.
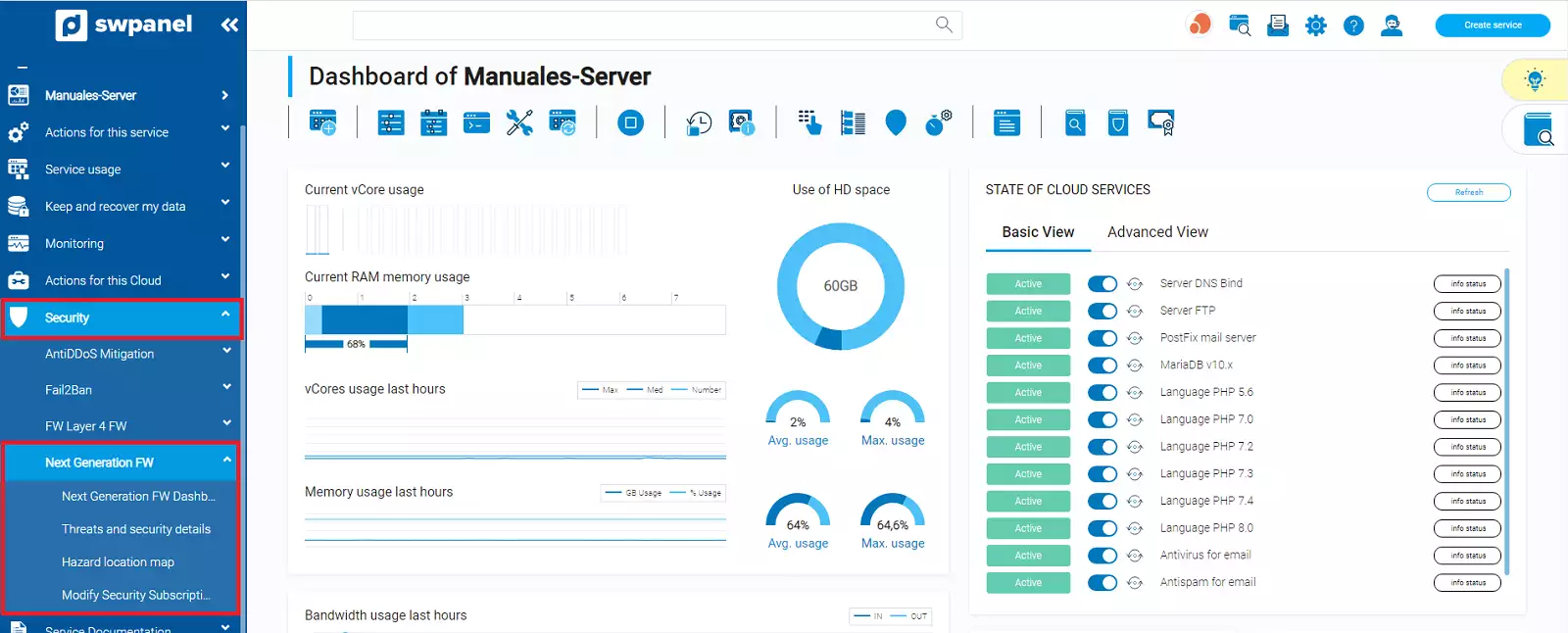
Also, in the Services tree, the services with Next Generation Security enabled appear with a shield icon on the left side of the service name and in the Manage menu, within the Security Services section, a new option Next Generation Security will appear which, when clicked, will take us to the Next Generation Security section of this service.
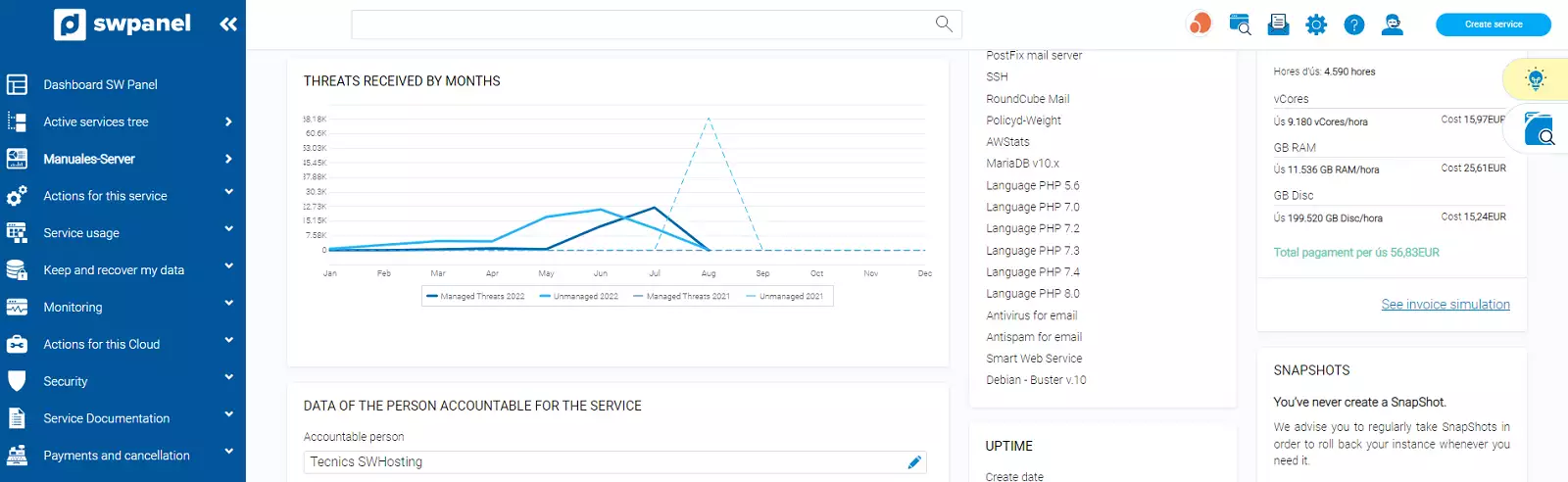
This Dashboard shows a summary of everything that is being detected in the outgoing and incoming traffic to your server or cloud and the actions that are being taken as a control measure.
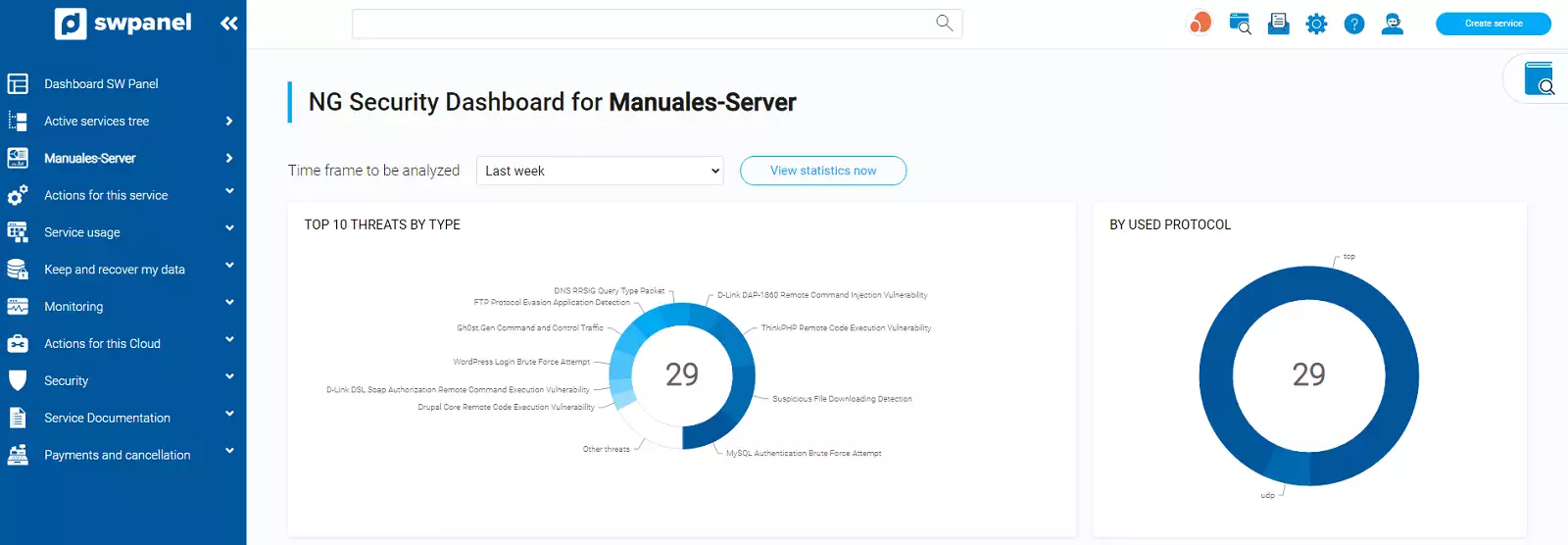
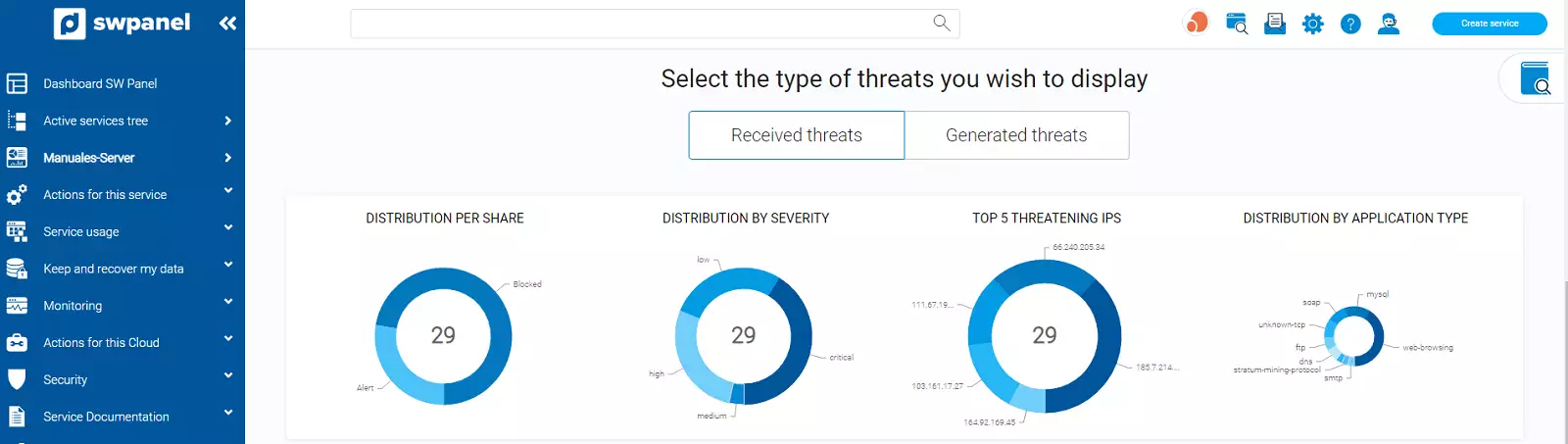
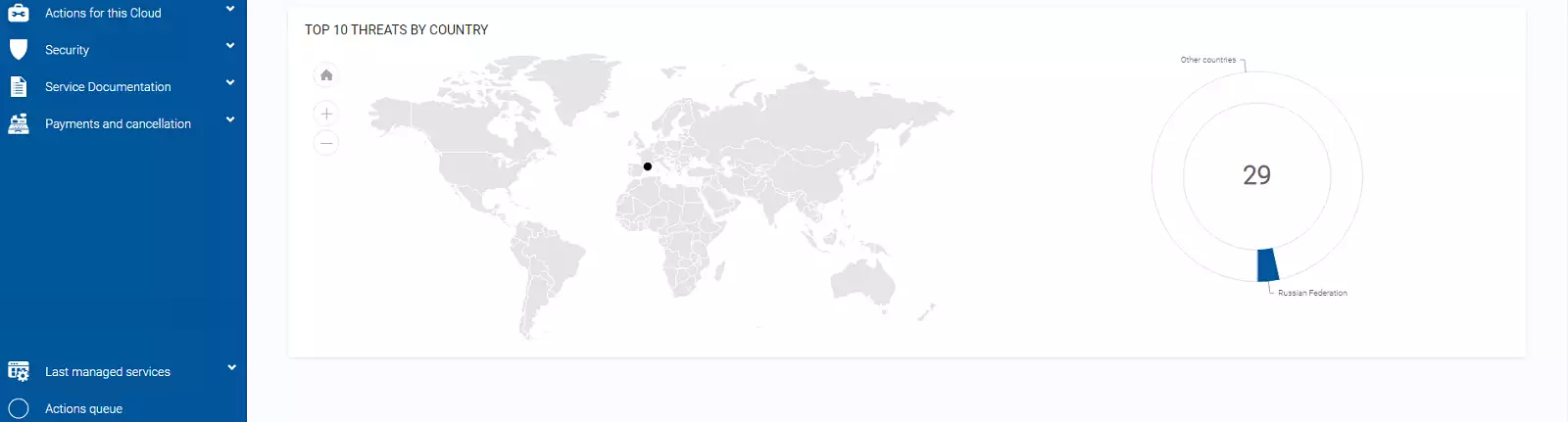
You will also find a map showing the geolocation of the sources of the attacks or the destinations of your attacks, in case it is your server or cloud that is the attacker.
At the top, you will find a drop-down menu that allows you to analyse the period you want. Select or indicate the period and the Dashboard will be reloaded with the data for that period.
When you activate Next Generation Security in your main SWPanel Dashboard, a new table will appear with a summary of the threats per month that Next Generation Security is dealing with in your services.
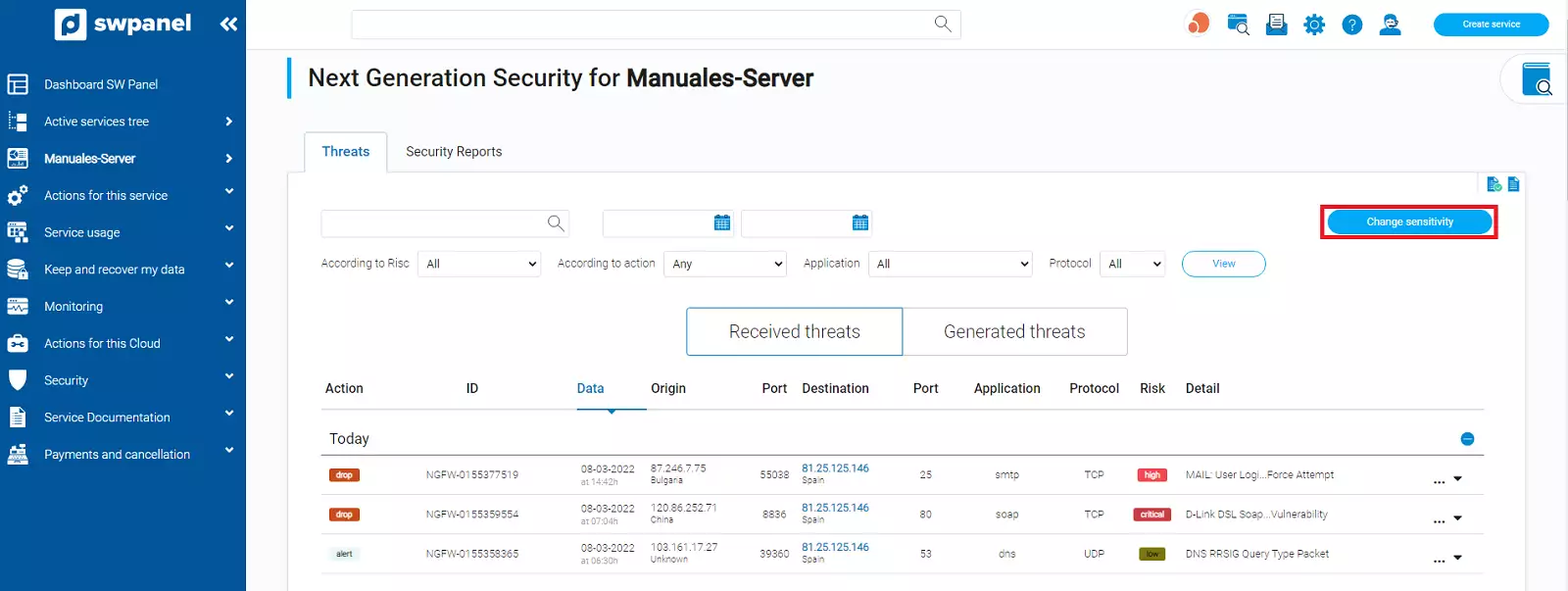
The threat list will show you all the threats detected by the Layer 7 Firewalls and the actions that have been taken on it.
There are always 2 possible actions to take:
This threat has been blocked and the service has been protected.
This threat has been allowed to pass as it is considered not harmful.
The actions to be taken and the severity or hardness of the analysis of these actions can be configured using the Change Sensitivity button.
You can define between 4 different sensitivities and adjust how you want the Firewall to scan for vulnerabilities.
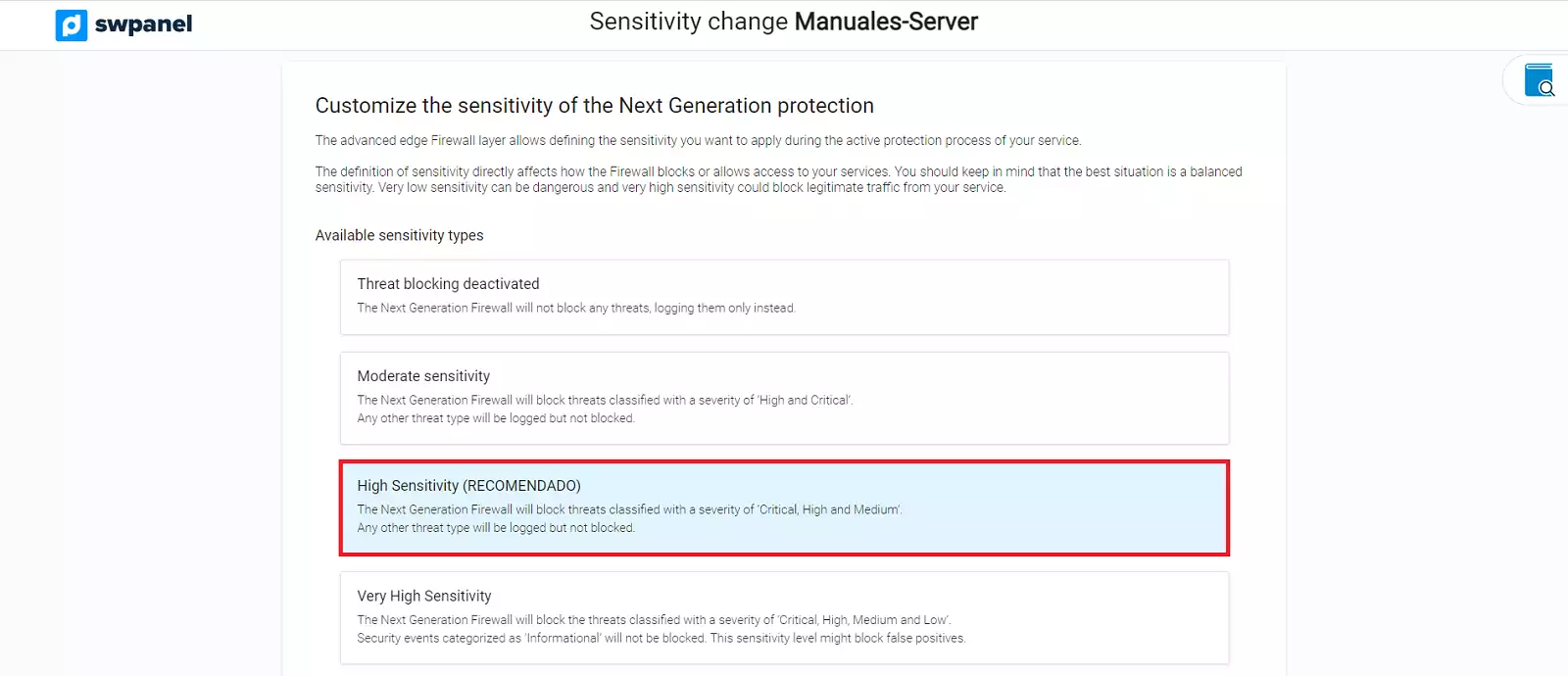
Simply check the box for the type of sensitivity you want and accept the change. Once this is done, the Firewall will automatically adjust to the sensitivity you have set as the working pattern.
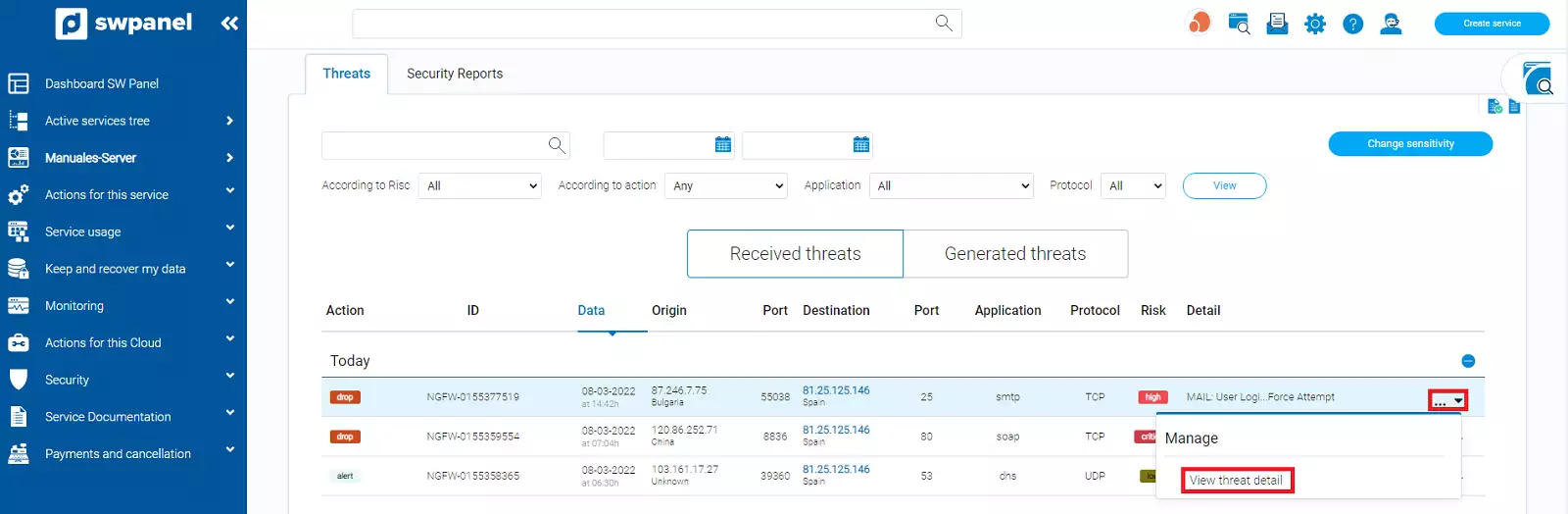
To facilitate the search for a specific threat, you have different filters in the list, including a text and date search engine that will allow you to adjust the search as much as possible.
Depending on the type of Next Generation security subscription you have in your service, the manage menu will show you more or less options.
Mainly, you should use it to be able to know in detail the threat that has been treated, to do this use the option View threat detail.
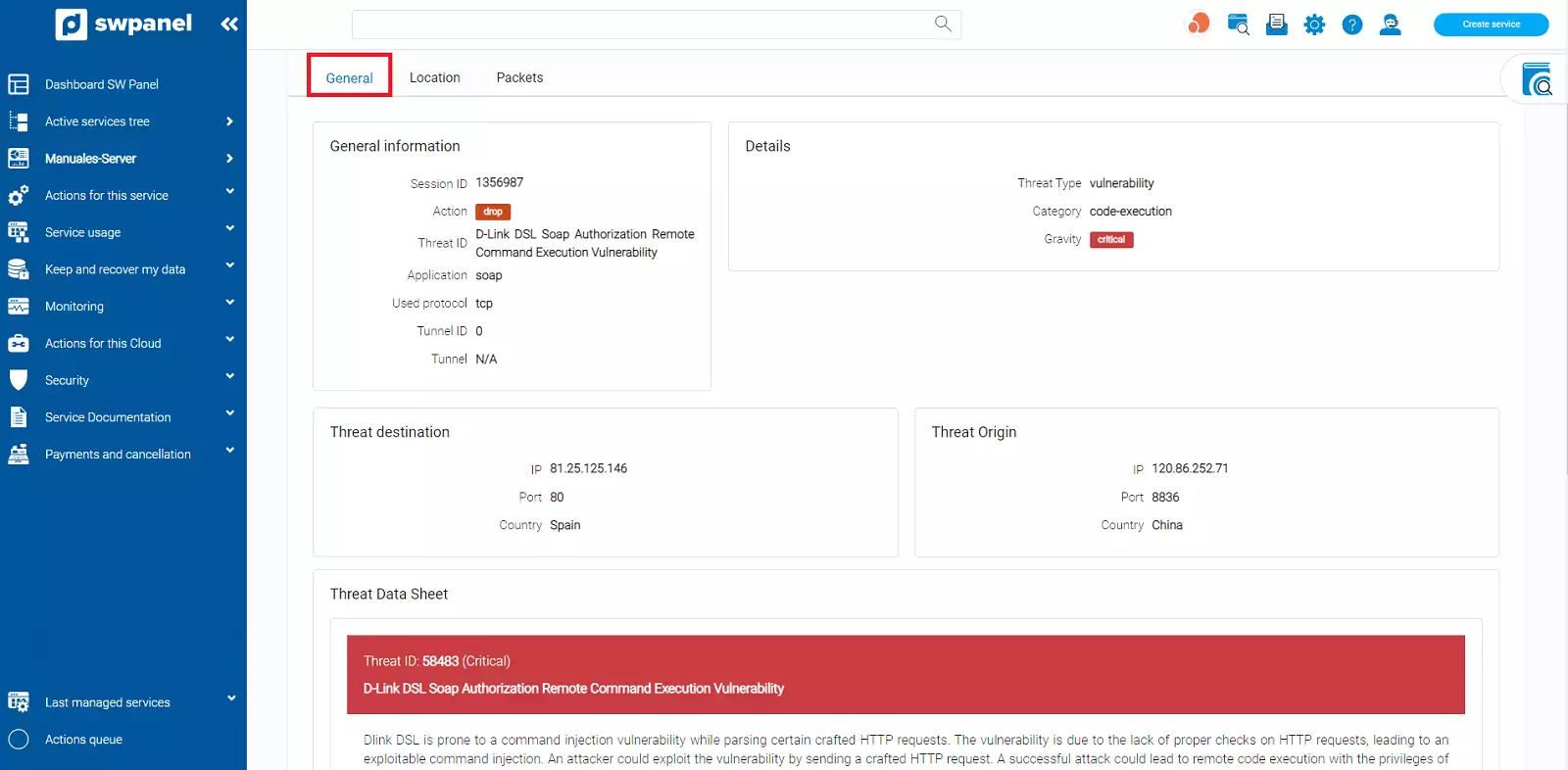
This option will show you all the details that are known about the threat you have selected.
The information is displayed sorted into 3 tabs which are:
General information about the threat, details of the threat, as well as origin and destination.
In case of a globally identified and classified threat, the DataSheet of the threat will be displayed, which is obtained through the CVE of the threat.
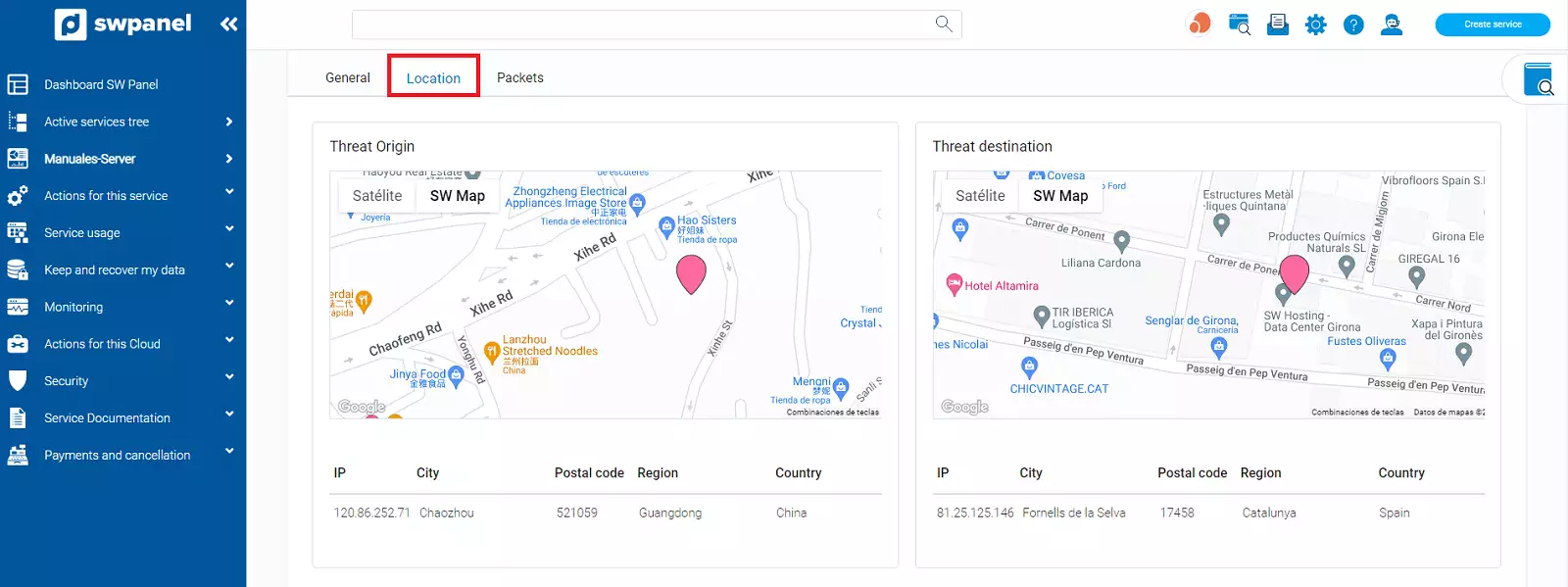
The determined location of the threat's source and destination IP is displayed on a map.
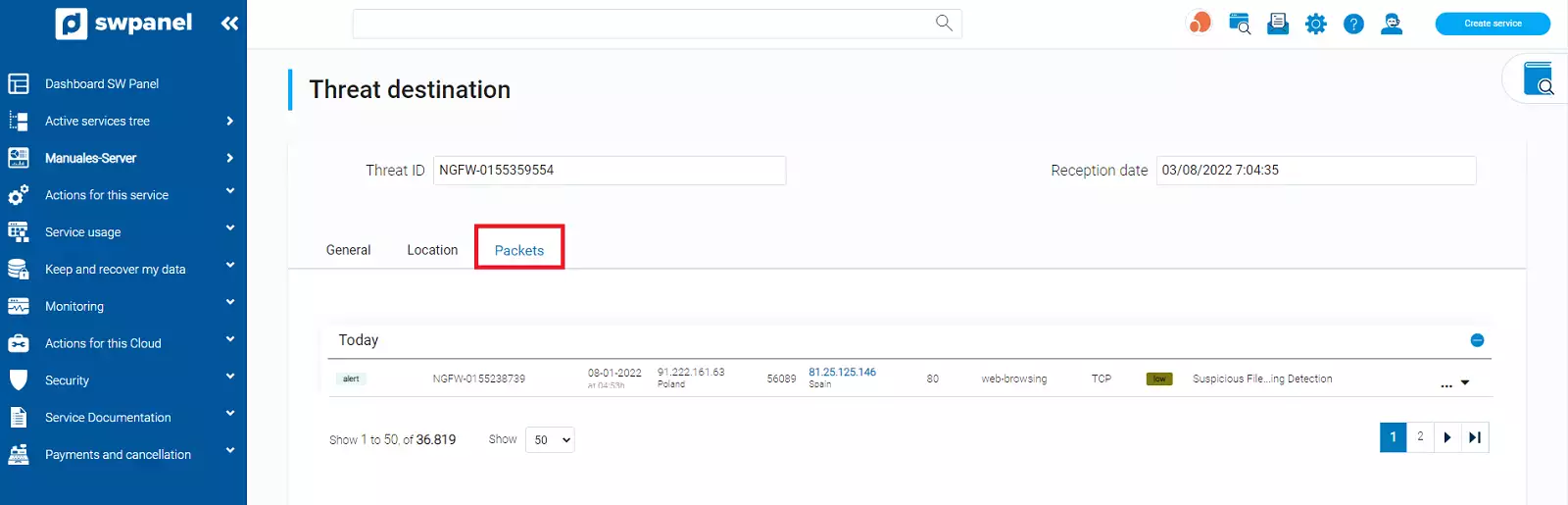
If specific traffic packets of this threat have been identified, they are listed in this tab as a listing
You can schedule automated reports to scan your Cloud for possible vulnerabilities.
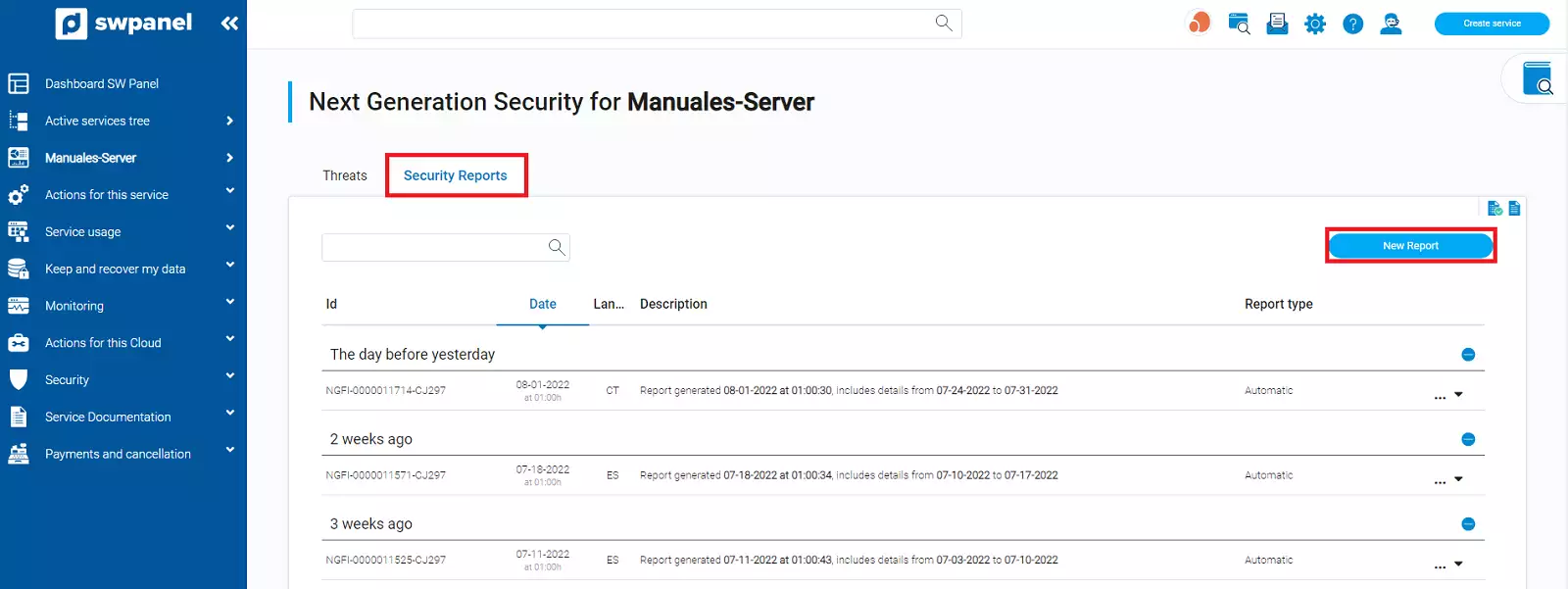
To do this, go to the Security Reports tab on the right side of Threats and you will see a list of all the reports you have created. In the right hand corner, there will be a blue button that will allow you to create new reports:
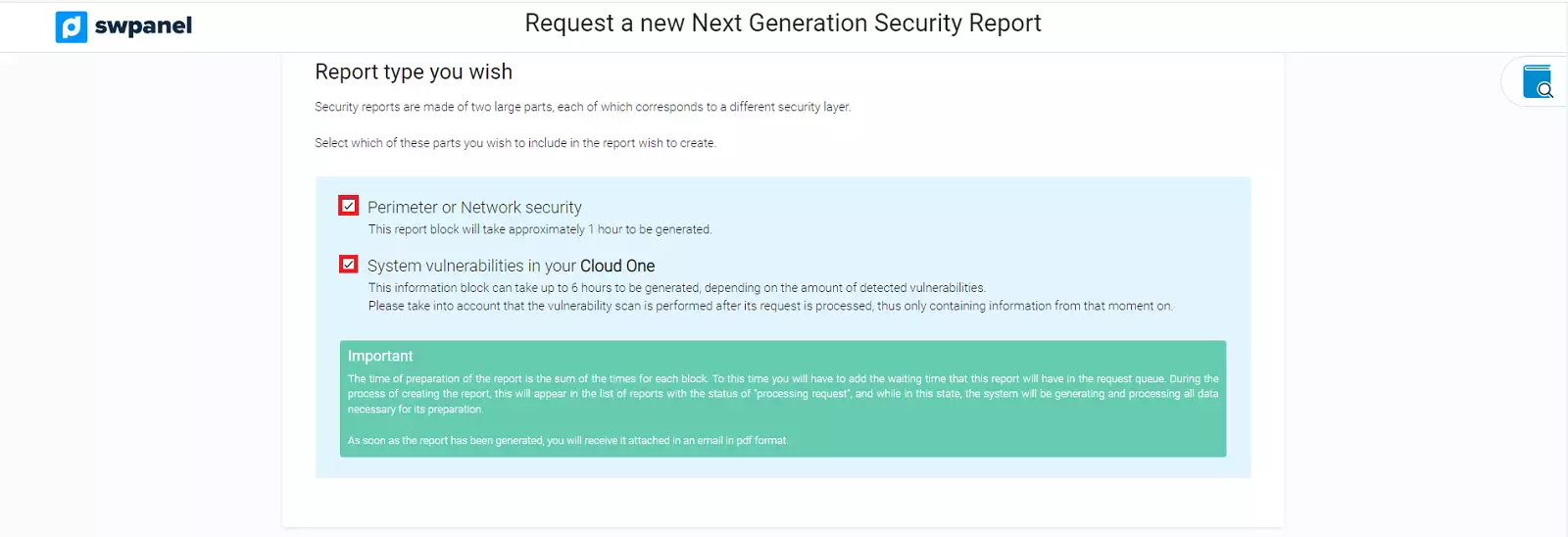
The screen that will appear will be divided into 3 blocks:
There are two types of reports available, Network or Perimeter Security and System Vulnerabilities of your Cloud One system.
In the scan you have to define which days you want to scan, choosing a start day and an end day, the panel itself will count the total days you will scan.
Please note that you can only scan a maximum of 30 days, and the start date cannot be earlier than 10-01-2020:
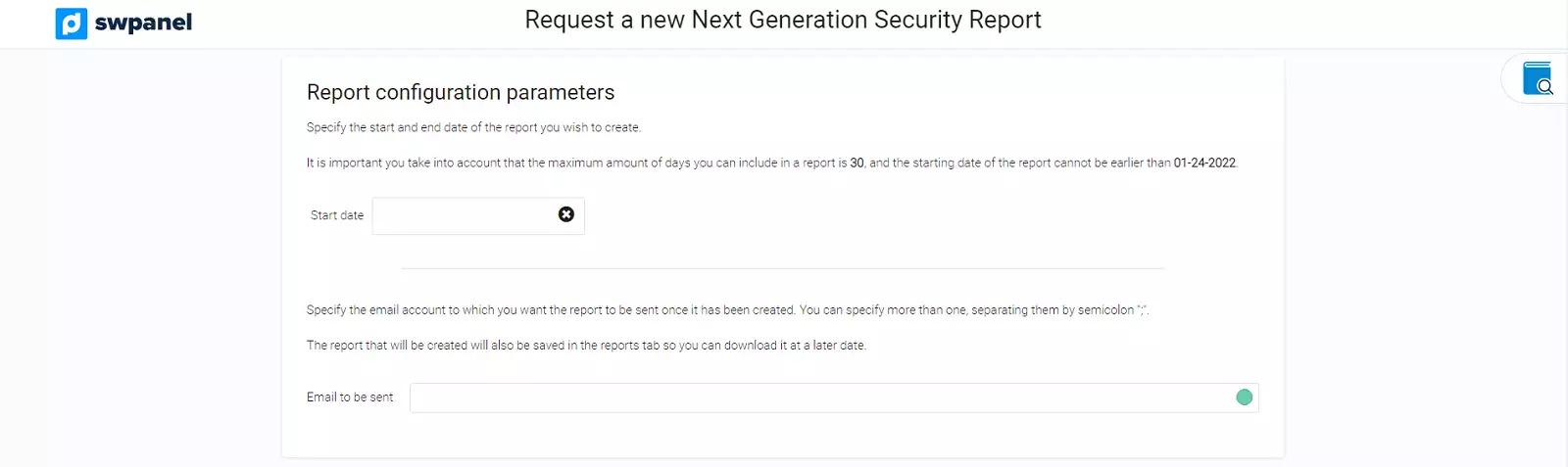
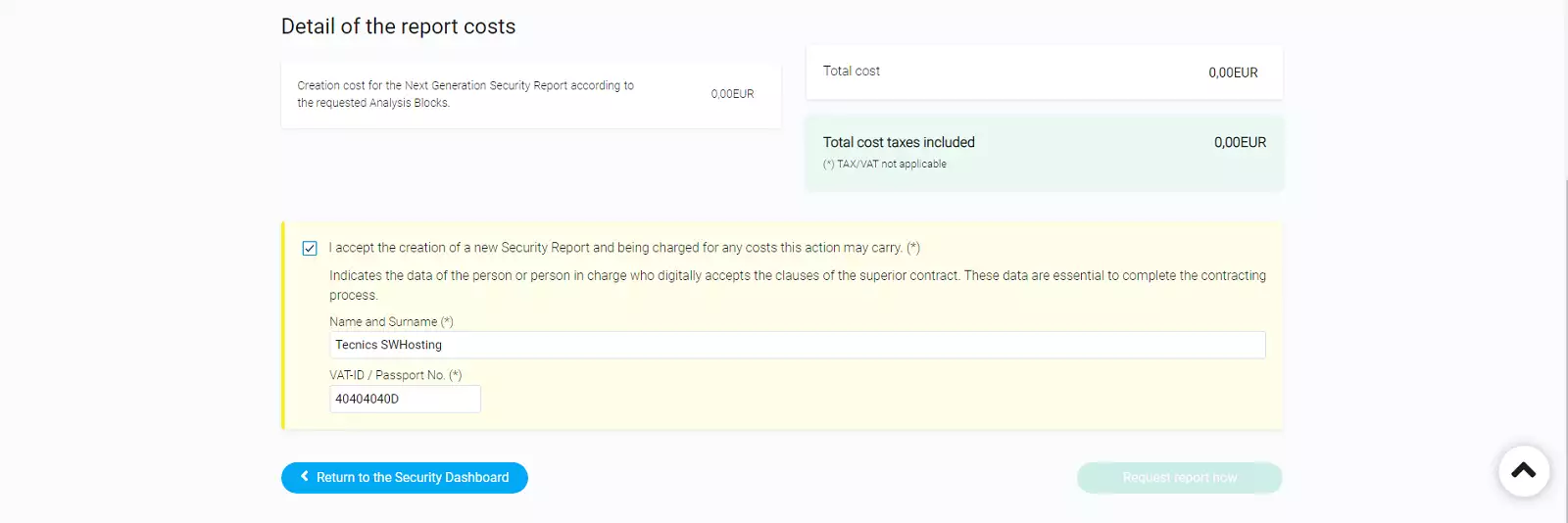
The last section will specify the costs of the report.